This post will show you how to install Kolab mail server on ubuntu 14.04, in this example on a DigitalOcean VPS. Kolab's recipient policy will be removed because I do not need guaranteed unique email addresses, secondary alias addresses setup etc. DKIM is another important factor when configuring a mail server as it allows other mail servers to validate the authenticity of you emails. There are many useful plugins available for roundcube such as integration with Google Authenticator app. For sources see the reference section at the end.
Install Kolab
The first step is to install Kolab on the VPS. Add the following to /etc/apt/sources.list.d/kolab.list using nano or similar.
deb http://obs.kolabsys.com/repositories/Kolab:/3.3/Ubuntu_14.04/ ./ deb http://obs.kolabsys.com/repositories/Kolab:/3.3:/Updates/Ubuntu_14.04/ ./
We need to import the authentication key to validate the packages. Run these commands.
gpg --search devel@lists.kolab.org gpg --export --armor devel@lists.kolab.org | apt-key add -
To make sure the Ubuntu server priorities the packages from the Kolab repository we need to create a preferences file. Create and put the following in /etc/apt/preferences.d/kolab:
Package: *
Pin: origin obs.kolabsys.com
Pin-Priority: 501Setup Kolab
Before running the setup tool the server MUST have its FQDN (Fully Qualified Domain Name) configured. To check run cat /etc/hosts
# Your system has configured 'manage_etc_hosts' as True. # As a result, if you wish for changes to this file to persist # then you will need to either # a.) make changes to the master file in /etc/cloud/templates/hosts.tmpl # b.) change or remove the value of 'manage_etc_hosts' in # /etc/cloud/cloud.cfg or cloud-config from user-data 127.0.1.1 mail.example.com mail.example.com 127.0.0.1 localhost # The following lines are desirable for IPv6 capable hosts ::1 ip6-localhost ip6-loopback fe00::0 ip6-localnet ff00::0 ip6-mcastprefix ff02::1 ip6-allnodes ff02::2 ip6-allrouters ff02::3 ip6-allhosts
Also run cat /etc/hostname which should show:
mail.example.com
Now we need to configure the Kolab server which is surprisingly easy because we can use the provided setup tool. Run the following command:
setup-kolab
This will launch a command line wizard asking some questions. You can either accept the generated answer in the square brackets by pressing enter or type in your own. Below are examples of the questions in order, when running the command an explanation of parameter is provided.
LDAP Admin User [ 93jef0fej09]: LDAP Directory Manager User [gsljgwbfi3u93rf3w]:
Please choose the system user and group the service should use to run under.
These should be existing, unprivileged, local system POSIX accounts with no
shell.
User [dirsrv]: Group[dirsrv]: Cyrus Administrator password [LwW_gjn645m46]: Kolab Service password [riY4t4ywe-dURe1]: MySQL kolab password [bFR43t4$DTojmx1]: Need to type out the timezone manually. Timezone ID [UTC]: Europe/London MySQL roundcube password [OH-zT66jhf6jnZKc]:
Remove Kolab Recipient Policy
Kolab has a recipient policy designed to generate the primary and secondary email addresses of the users based on their first and last names, this would obviously be useful in an enterprise environment however within a personal or small business environment then it could become annoying. Kolab does allow the creation of more alias addresses but the user would have 3 generated already. I wanted to specify my own primary email address and create as many or as little aliases as I wanted.
Firstly edit this file: /etc/kolab/kolab.conf
Remove these lines from around line 8:
primary_mail = %(surname)s@%(domain)s
secondary_mail = {
0: {
"{0}.{1}@{2}": "format('%(givenname)s'[0:1].capitalize(), '%(surname)s', '%(domain)s')"
},
1: {
"{0}@{1}": "format('%(uid)s', '%(domain)s')"
},
2: {
"{0}@{1}": "format('%(givenname)s.%(surname)s', '%(domain)s')"
}
}Right at the bottom of the file is a section with your domain name:
[example.com] default_quota = 1048576 primary_mail = %(givenname)s.%(surname)s@%(domain)s //Remove this line
Then restart the service:
service kolab-server restart
Now we need to copy a template file, modify it and then run the file to modify the current Kolab installation. This can be a bit tricky to remove exactly the right things, I have missed one line and then could not add more than one alias address as the plus button had been removed.
Run this command to copy the template file.
cp /usr/share/doc/kolab-webadmin/sample-insert-user_types.php.gz /usr/share/kolab-webadmin/
Move to the directory with the cd command and unzip the file with:
gunzip sample-insert-user_types.php.gz
Edit the PHP Template file
Edit these lines as directed:
$attributes = Array( "auto_form_fields" => Array( // Note that this form field is marked as optional in // 'form_fields'. "alias" => Array( "type" => "list", //Remove "data" => Array( //Remove "givenname", //Remove "preferredlanguage", //Remove "sn", //Remove ), //Remove ), "cn" => Array( "data" => Array( "givenname", "sn", ), ), "displayname" => Array( "data" => Array( "givenname", "sn", ), ), "mail" => Array( "data" => Array( //Remove "givenname", //Remove "preferredlanguage", //Remove "sn", //Remove ), //Remove ),
It should like:
$attributes = Array( "auto_form_fields" => Array( // Note that this form field is marked as optional in // 'form_fields'. "alias" => Array( ), "cn" => Array( "data" => Array( "givenname", "sn", ), ), "displayname" => Array( "data" => Array( "givenname", "sn", ), ), "mail" => Array( ),
Now further down the file we need to add some extra lines:
"form_fields" => Array(
"alias" => Array(
"optional" => true,
"type" => "list" //Very important, without this then you wont be able to add more than one alias address
),
"givenname" => Array(),
"initials" => Array(
"optional" => true,
"Type" => "list"
),
//Add the below mail section
"mail" => Array(
"optional" => true
),
Save the file and then check for syntax errors:
php -l sample-insert-user_types.php
Apply the changes to the Kolab installation:
php sample-insert-user_types.php
Access Kolab Webmail top level domain
The default behaviour of Kolab is to provide the webmail access at mail.example.com/webmail or mail.example.com/roundcubemail which I don't want. To access webmail at mail.example.com then it is a simple edit of the apache2 site configuration.
Edit /etc/apache2/sites-enabled/roundcubemail.conf
Find the following lines:
Alias /roundcubemail /usr/share/roundcubemail/public_html/ Alias /webmail /usr/share/roundcubemail/public_html/
Replace the above lines with this one. Basically we are removing the /roundcubemail or /webmail of the above lines.
Alias / /usr/share/roundcubemail/public_html/
Restart Apache2:
service apache2 restart
I would like to change the default /kolab-webadmin to just admin but when I tried the same approach I got errors after logging in so I might come back to that at a later date.
Postgrey/Virus/Spam
Post grey is a very useful way of stopping spam emails. Here is a good explanation of Greylisting from Kolab Blog.
"Stopping spam before it enters the queue is a good thing. One way to achieve this is Greylisting: Reject a triplet (sending host, sender address, recipient address) on the first deliver attempt with a temporary error (450 4.2.0 <tobias@tobrunet.ch>: Recipient address rejected: Greylisted, see http://postgrey.schweikert.ch/help/tobrunet.ch.html) and save this triplet. On the second delivery attempt check the triplet against the database and if it matches, allow this message to be delivered. This stops many spam senders because they only try it once. A correctly configured MTA tries it again after a few minutes and the mail is delivered."
Enable postgrey by editing the /etc/postfix/main.cf file:
# "check_policy_service inet:127.0.0.1:10023" enables Postgrey. smtpd_recipient_restrictions = permit_mynetworks, reject_unauth_pipelining, reject_rbl_client zen.spamhaus.org, reject_rbl_client sbl.spamhaus.org, reject_rbl_client blackholes.easynet.nl, reject_rbl_client dnsbl.njabl.org, reject_non_fqdn_recipient, reject_invalid_helo_hostname, reject_unknown_recipient_domain, reject_unauth_destination, check_policy_service unix:private/recipient_policy_incoming, check_policy_service inet:127.0.0.1:10023, //Added to enable postgrey permit
Enable Anti-Virus and SpamAssassin
Edit /etc/amavis/conf.d/15-content_filter_mode
# # Default antivirus checking mode # Please note, that anti-virus checking is DISABLED by # default. # If You wish to enable it, please uncomment the following lines: @bypass_virus_checks_maps = ( \%bypass_virus_checks, \@bypass_virus_checks_acl, \$bypass_virus_checks_re); # # Default SPAM checking mode # Please note, that anti-spam checking is DISABLED by # default. # If You wish to enable it, please uncomment the following lines: @bypass_spam_checks_maps = ( \%bypass_spam_checks, \@bypass_spam_checks_acl, \$bypass_spam_checks_re);
Un-comment the appropriate lines in the above file to enable anti-virus/spam checking.
Add the users to the correct groups:
adduser clamav amavis adduser amavis clamav
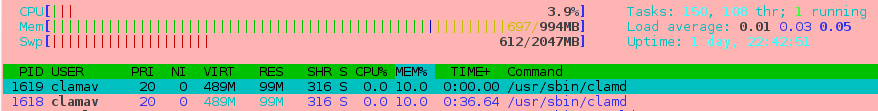
Please note that the clamav daemon uses around 200MB for each instance and won't run on a VPS with less than 1Gb and on a 1GB needs a swap partition to be able to restart the service.
Create SWAP File
We are using a VPS from DigitalOcean and this does not have a swap partition assigned to it however we can just create a swap file instead, as DigitalOcean use SSDs for their storage then the swap file is pretty quick.
Create a file called swapfile in the root file system.
fallocate -l 2048M /swapfile
Check to see if the file has been created.
ls -la / -rw-r--r-- 1 root root 2147483648 Oct 13 19:20 swapfile
Set the correct permissions.
chmod 600 /swapfile ls -la / -rw------- 1 root root 2147483648 Oct 13 19:20 swapfile
Format it as a SWAP type.
mkswap /swapfile Setting up swapspace version 1, size = 2097148 KiB no label, UUID=59661226-6b9d-419d-a39c-6a81b3928af9
Activate the SWAP file so it is used as SWAP, you should see SWAP available in htop after running this command.
swapon /swapfile
Edit the Fstab to enable the swap partition on boot.
/swapfile none swap defaults 0 0
Now clamav will restart correctly because it can allocate the memory.
POODLE Attack Revealed, Disable SSLv3
Information from BetterCrypto.
Edit the Postfix Main.cf
Change the TLS section to:
# TLS parameters
#smtpd_tls_cert_file=/etc/ssl/certs/ssl-cert-snakeoil.pem #smtpd_tls_key_file=/etc/ssl/private/ssl-cert-snakeoil.key
smtpd_tls_cert_file=/etc/apache2/ssl/ssl.crt
smtpd_tls_key_file=/etc/apache2/ssl/private.key
smtpd_tls_CAfile=/etc/apache2/ssl/sub.class1.server.ca.pem
# enable opportunistic TLS support in the SMTP server and client
#smtpd_use_tls=yes //I think this is no longer used
smtp_tls_security_level = may
smtpd_tls_security_level = may
# if you have authentication enabled, only offer it after STARTTLS
smtpd_tls_auth_only = yes
tls_ssl_options = NO_COMPRESSION
smtpd_tls_mandatory_protocols = !SSLv2, !SSLv3
smtpd_tls_mandatory_ciphers=high
tls_high_cipherlist=EDH+CAMELLIA:EDH+aRSA:EECDH+aRSA+AESGCM:EECDH+aRSA+SHA384:EECDH+aRSA+SHA256:EECDH:+CAMELLIA256:+AES256:+CAMELLIA128:+AES128:+SSLv3:!aNULL:!eNULL:!LOW:!3DES:!MD5:!EXP:!PSK:!DSS:!RC4:!SEED:!ECDSA:CAMELLIA256-SHA:AES256-SHA:CAMELLIA128-SHA:AES128-SHA
smtpd_tls_eecdh_grade=ultra
smtpd_tls_session_cache_database = btree:${data_directory}/smtpd_scache
smtp_tls_session_cache_database = btree:${data_directory}/smtp_scacheEdit the /etc/cyrus.conf
If you don't need or use Pop3 then it may as well be disabled.
# pop3 cmd="pop3d" listen="pop3" prefork=3 # pop3s cmd="pop3d -s" listen="pop3s" prefork=1
Edit /etc/imapd.conf
tls_cert_file: /etc/apache2/ssl/ssl.crt tls_key_file: /etc/apache2/ssl/private.key tls_ca_file: /etc/apache2/ssl/sub.class1.server.ca.pem # The list of SSL/TLS ciphers to allow, in decreasing order of precedence. # The format of the string is described in ciphers(1). The Debian default # selects TLSv1 high-security ciphers only, and removes all anonymous ciphers # from the list (because they provide no defense against man-in-the-middle # attacks). It also orders the list so that stronger ciphers come first. tls_cipher_list: EDH+CAMELLIA:EDH+aRSA:EECDH+aRSA+AESGCM:EECDH+aRSA+SHA384:EECDH+aRSA+SHA256:EECDH:+CAMELLIA256:+AES256:+CAMELLIA128:+AES128:+SSLv3:!aNULL:!eNULL:!LOW:!3DES:!MD5:!EXP:!PSK:!DSS:!RC4:!SEED:!ECDSA:CAMELLIA256-SHA:AES256-SHA:CAMELLIA128-SHA:AES128-SHA
Configure DNS/SPF (Important for a trusted mail server)
Please look at this post about DNS configuration.
Adding Plugins to Roundcube
Adding plugins is quite simple. Please do not confuse myRoundcube with roundcube as these are not the official plugins, they are modified versions that require the use of their plugin manager and they also charge for some of the plus versions of plugins. This is not to say do not use them as many people do but I prefer not to be forced to use a tool just to install and get the plugins.
On roundcubes official wiki they mention the main.inc.php file but in the Kolab install it is /usr/share/roundcubemail/config/config.inc.php instead.
My favourite plugins so far are: markasjunk2 , serverinfo and twofactor_gauthenticator.
The way to install a plugin is to copy the plugin the correct directory and then enable it in the plugin array. You don't even need to restart any services, just refresh the page. The links above have instructions on installation but I will go through install the serverinfo plugin. This plugin adds useful information to your settings page such as port numbers etc.
Download the zip/tar file to a directory on the server using wget.
wget http://axel.sjostedt.no/misc/files/rcube_plg_serverinfo.tar.gz
Unzip the file:
gunzip rcube_plg_serverinfo.tar.gz tar -xvf rcube_plg_serverinfo.tar
Copy the folder to the plugin directory:
cp -R serverinfo /usr/share/roundcubemail/plugins/
Edit this file /usr/share/roundcubemail/config/config.inc.php and find the plugin section. I have removed most from this list as it is a little long and not necessary to show the whole list.
// Plugins
$config['plugins'] = array(
'kolab_auth',
'calendar',
'jqueryui',
'serverinfo',
// contextmenu must be after kolab_addressbook (#444)
'contextmenu',
);I have added the plugin serverinfo. Generally the plugin name is the name of folder copied. Please note, When downloading some of the plugins from Github the folder normally needs to be renamed as per the instructions.
Now the plugin is enabled.
References
Kolab Installation Guide | Kolab.org
Roundcube Plugin Repository | Roundcube.net
DKIM Configuration | Exratione

Comments powered by Disqus.