This will show you how to setup horde to log failed logins and use fail2ban to detect these. A useful tool to check if any fail2ban filters are working as expected is the fail2ban-regex tool, more details here Fail2ban-regex help.
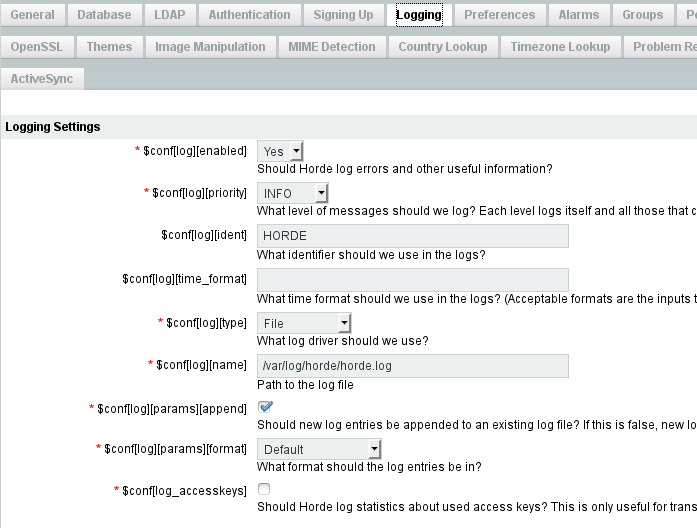
Login to horde webmail using an admin account. Navigate to the configuration page -> horde -> logging tab. You should see something similar to this.
Create the directory and file specified in the configuration page.
mkdir /var/log/horde chown -R root:www-data /var/log/horde/ chmod 770 /var/log/horde/ touch /var/log/horde/horde.log
Check the permissions are correct.
ls -l /var/log/horde/
Run the following command to 'follow the file' and login to horde. You should see some messages about a successful or failed login.
tail -f /var/log/horde/horde.log
Create the following file, this is the filters file which is what fail2ban uses to match suspicious activity in the log files.
nano /etc/fail2ban/filter.d/horde.conf
Add the following to it:
[Definition] failregex = FAILED LOGIN for *.*\[<HOST>\].*$ ignoreregex =
Create or modify the jail.local file under /etc/fail2ban/ Add the following 'jail', these use the filters to match the suspicious activity in the specified log files, they then perform the actions specified or the default if none are specified in the jail.
[horde] enabled = true port = http,https filter = horde logpath = /var/log/horde/horde.log
Test
tail the horde log file as shown earlier, try logging in to the horde webmail with incorrect credentials, repeat this several times and you should see this being recorded in the log messages. Depending on the number of allowed attempts specified in the jail.conf it should ban your IP after exceeding the allowed amount.

Comments powered by Disqus.